For the purposes of this post, let's assume that you're running an out-of-the-box installation of OpenSSH server on a linux system, with the configuration files located in the /etc/ssh directory. The most useful parameter in the /etc/ssh/sshd_config file is the "Port" setting. By default, it's set to 22, which is the standard port for ssh. In most situations where your web browsing traffic is being filtered, port 22 is likely being blocked as well, so that doesn't help us too much. You can change the line to
- Port 443
- Protocol 2
- This is to ensure that your ssh server only uses the latest, more secure protocol, as backwards compatibility with protocol 1 introduces vulnerabilities into the system
- PermitRootLogin no
- This is to ensure that nobody can login remotely as root directly. An attacker would need to first gain access to a lower privileged account, and then attempt to escalate from there.
Once you've got the sshd_config file all set, save it, and restart the sshd service. Then you should be ready to login remotely using any ssh client. For our example here, we'll use a popular one called PuTTY. Once you've downloaded, and optionally installed, PuTTY, fire it up, and when the Configuration window comes up, enter in the hostname/IP address of your ssh server, with the port that you selected in your sshd_config file:
Then, on the left-hand side, under Category, navigate to Connection --> SSH --> Tunnels. Enter in a Source port for the tunnel (I've chosen 1080 because the tunnel is really creating a SOCKS proxy, which uses 1080 by default), select the radio button for Dynamic instead of Local, and click the Add button next to the Source port field. It should now look something like this:
At this point you can go back to Category --> Session, and save the session so that you won't need to configure it all again, or you can just click the Open button in the lower-right corner to start up your ssh session. Once you've got your session up and running, you'll need to configure your browser of choice to take advantage of the tunnel you've just created.
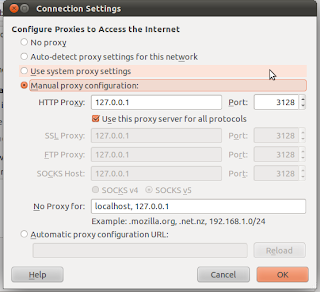
In IE9, navigate to Internet Options --> Connections --> LAN Settings --> Proxy server, Check the box for "Use a proxy server for your LAN," and click the Advanced button. In the Proxy settings window that comes up, for the "Socks:" entry, enter in 127.0.0.1 for the address and 1080 for the port. Click on the OK button when you're done.
In Firefox 5, navigate to Options --> Advanced --> Network --> Settings... Select Manual proxy configuration, and for the "SOCKS Host:" entry, enter in 127.0.0.1 and 1080 for the Port. Select the radio button for SOCKS v5 instead of v4. Click on the OK button when you're done.
In Chrome 12, navigate to Options --> Under the Hood --> Network --> Change proxy settings... This will bring up the same window as for IE9 above, so just configure the Proxy server as mentioned previously.
You should now be all set! Any web browsing that you attempt to do now will be redirected through your encrypted ssh tunnel, and go out to the Internet from the network that your ssh server resides on, rather than the current network that you're connected to locally. Filters schmilters!
This technique has an infinite number of uses for getting you where you need to go. You can tunnel things like Microsoft Remote Desktop/Terminal Services, port 3389, Instant Messaging, VNC/Apple Remote Desktop, port 5900, etc. Best of all, it's all encrypted, and potentially performs better than a direct connection, as you can even turn on compression for the SSH connection.
To perform simple port forwarding for these types of services, you'll need to add another tunnel into your PuTTY session configuration. This time, select the radio button for Local instead of Dynamic. You'll also need to enter in a specific destination host and port to forward the traffic to on the other side of the tunnel. For example, say you want to connect to a Windows system that has an IP address of 192.168.1.2 on the remote network, using Remote Desktop, you would set up the tunnel in PuTTY like so:
Then, once your ssh session is up, in your Remote Desktop Connection client window, simply connect to 127.0.0.1:3389 to utilize the tunnel to get to the remote host:
You may run into issues if you're trying to do this from a Windows system that is itself also accessible via Remote Desktop, meaning port 3389 on localhost is already taken. In that case, just change the source port to something else like 3391 in the port forwarding configuration, and connect to 127.0.0.1:3391 from your RDP client, easy as that.
And of course, for those of you that are like me and prefer to use the command-line for things like this, a simple ssh one-liner using something like cygwin:
- ssh -p443 -D1080 -L3391:192.168.1.2:3389 username@your-ssh-server
does the exact same thing as all that GUI PuTTY configuration.
Happy tunneling!